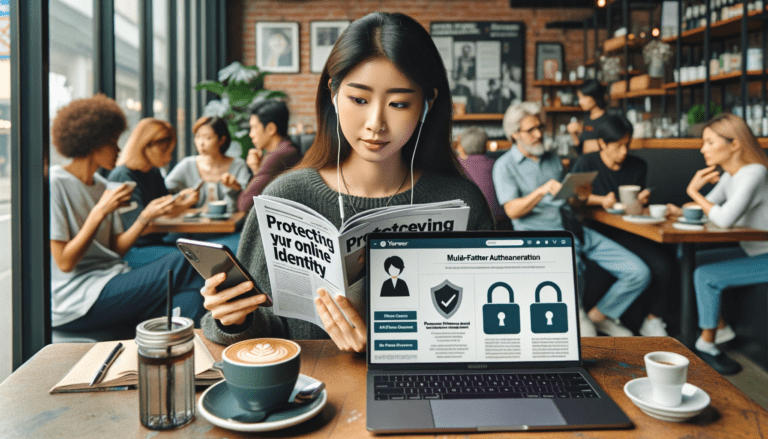
In today's world, a person's online identity is a direct extension of their personal identity. As we transition to an ever-increasing virtual world, our lives are expanding into the digital space, where our personal data is just as precious as physical assets. People share a significant portion of their lives online - from social connections to financial transactions, making it imperative to protect personal information from any potential threats.
Identity theft is a growing concern in the digital age. Cybercriminals are continuously evolving their techniques to trick people into revealing sensitive information. From online scams to sophisticated phishing attacks, the Internet has become a battlefield where the war for information is relentlessly waged. Safeguarding your personal and online identity is more important than ever, and it is essential to familiarize yourself with the necessary precautions to ensure your safety in the digital realm.

Understanding Identity Theft and Online Scams
Identity theft is a serious crime that occurs when someone steals your personal information, such as your Social Security Number, to commit fraudulent activities. This could possibly be credit fraud, where the thief opens a new account in your name and racks up substantial debt, or tax-related fraud, when the offender uses your stolen Social Security Number to file a tax return and claim a fraudulent refund. When your identity is stolen, it takes a toll both financially and emotionally, and recovery can be lengthy and stressful.
Online scams, on the other hand, include a variety of deceptive tactics implemented through the internet. These tactics, ranging from fraudulent emails asking for personal information to fake websites appearing legitimate, aim to trick you into revealing your personal data. Phishing scams, for example, send deceptive emails appearing to be from trustworthy organizations or businesses but direct you towards spoofed websites to steal your information. Being aware of such scams and understanding the potential threats is key to protecting your identity and maintaining your online safety.
Definition and Implications of Identity Theft
Identity theft, often executed digitally, is a growing concern in today's tech-focused world. It refers to the deliberate use of someone else's identifying information, usually to gain a financial advantage or obtain credit, in most cases, slyly and without the knowledge of the victim. This deceiving act is not limited to stealing someone's name; it may extend to pilfering financial information, social security number, or even medical data.
This fraudulent crime holds severe implications for the victims, leading to long-term financial and credibility issues, often taking years to resolve completely. A common way that identity thieves gain access is through weak or easily guessed passwords. Therefore, maintaining strong, unique passwords is imperative in safeguarding one's identity. The loss of financial information can lead to unauthorized transactions, resulting in the victim losing funds and tarnishing their credit history. Consequently, it is indubitably essential to raise awareness about this crime and promote comprehensive protective measures.

Common Online Scams: Phishing, Fraud, and Telephone Scams
The digital realm is replete with various forms of scams designed to trick users into revealing sensitive information or transferring money to fraudulent actors. Among these online deceptions, phishing, fraud, and telephone scams are some of the most common and damaging. They mainly capitalize on human error and often exploit weaknesses in mobile device security.
In phishing scams, fraudulent emails or messages masquerade as legitimate communications from reputable sources, encouraging recipients to click on embedded links. Once the link is clicked, personal information is unwittingly divulged or malware is installed on the user's device. Fraudulent scams are usually more elaborate, involving fake lotteries, fake charities, or painstakingly forged business opportunities. In telephone scams, callers pretend to be representatives of trusted entities like tax agencies or banks and seek sensitive information. Anti-virus software, along with sensible online practices, can significantly mitigate the risk posed by these scams, though vigilance remains the user's best defense.
REAL TIME CASE STUDIES FACTS AND FIGURES
| Category | Fact/Figure | Source |
|---|---|---|
| Global Cybercrime Costs | Cost of Cybercrime in 2023: $8 trillion | Forbes |
| Projected Cost of Cybercrime by 2025: $10.5 trillion | Forbes | |
| Cybersecurity Trends | Cyberattacks Initiated via Email: Over 75% | Norton |
| Daily Internet Crime Complaints: Over 2,000 in 2020 | Norton | |
| Remote Work and Cybersecurity | Organizations with Remote Workforce: 57% (work remotely at least two days a week) | Varonis |
| Employees Falling for Phishing Scams: 47% (cited distractions at home) | Varonis | |
| Automation and AI in Cybersecurity | Breach Identification and Containment: 28 days faster with AI and automation programs | Varonis |
| Third-party and Supply Chain Attacks | Varonis | |
| Users' PII Leaked in 2021 | 1.5 billion (due to third-party breaches) | Varonis |
Protecting Personal Information
The exposure of personal details in the digital world has become more common with the rise of social media platforms. Social Media Security thus plays a crucial role in the prevention of identity theft. It's important to critically assess what information you're sharing online and with whom. For instance, often, social media accounts are made with the user adding much more information than what is truly required, basis past experiences of platform usage. This could include the likes of - Full names, addresses, telephone numbers, and other identifying details. Sharing such information without caution can make you an easy target for online fraud.
In an effort to further fortify personal security on the internet, it's advisable to boost privacy settings across platforms where personal information is shared. This allows for control over the visibility of information to others. One effective approach to combat fraud is by employing two-factor authentication wherever possible. This feature requires users to provide two different verification methods, considerably impeding the attempts of cybercriminals to access personal details. Always remember, keeping personal information protected is the first line of defence against online scams and identity theft.
Safeguarding Your Social Security Number
Scams involving personal information are becoming increasingly prevalent in our ever-connected world. One such method utilized by these fraudsters involves direct attempts to breach what should be one of your most closely guarded secrets: your Social Security Number. Various tactics are applied by these unscrupulous individuals, including, but not limited to, telephone scams where the caller impersonates a government official demanding immediate disclosure of your Social Security Number.
Awareness of these tactics is paramount for individuals to fend off such invasive attempts. Always remember that legitimate government officials will seldom, if ever, call demanding your Social Security Number. In fact, sharing this vital number over the phone should be avoided entirely, unless you initiated the call and have full trust in the person or entity on the other end. It is essential to treat our Social Security Numbers with the utmost care to ensure our personal information remains secure.
Here are some steps you can take to safeguard your Social Security Number:
- Never share your Social Security Number over the phone unless you initiated the call and trust the other party completely.
- Be cautious of any emails or text messages asking for your personal information, particularly those claiming to be from government agencies. Legitimate bodies will rarely, if ever, request this kind of information through these channels.
- Always verify the identity of anyone who requests your Social Security Number. If in doubt, do not hesitate to ask them for their name, position and a contact number where they can be reached later.
- Regularly monitor all financial accounts linked with your Social Security Number. Look out for any suspicious activity that may indicate someone else is using it illicitly.
- Consider investing in an identity theft protection service. These services monitor various databases and alert you if someone tries to use your Social Security Number fraudulently.
By following these guidelines and remaining vigilant about protecting our personal information, we can significantly reduce our risk of falling victim to scams involving our Social Security Numbers. It's important not just for ourselves but also as part of collective efforts against cybercrime which ultimately affects us all.
Responsible Handling of Financial Information
We carry our lives in our wallets and online. From bank accounts to retirement plans, credit cards to social security numbers, a person is closely tied to their financial information. To safeguard your financial health, practices of responsible handling are pivotal. One crucial aspect in this is how you can effectively protect your online identity. Striving to keep your essential data secure from cyber criminals should always be a part of your financial strategy.
The world of internet banking and online transactions has transformed dramatically, making financial management, transfers and shopping convenient than ever before. With these convenience perks comes a potential downside - the risk of theft or compromise. Online security is more than just installing the latest anti-virus software. It's about understanding the value of one's personal financial data and taking active measures to protect it. These include carefully managing login credentials, using secure networks when performing transactions, and monitoring account activity for any potential signs of unauthorized activity.
Shredding Documents Containing Personal Information
The safeguarding of personal information requires more than just strong passwords and digital fortifications. It is easy to overlook the threat that physical documents pose, especially those containing sensitive information. Papers like bank statements, utility bills, health records, or old credit cards can turn into gold mines for identity thieves if they fall into the wrong hands. That's why a proactive method for ensuring these documents don’t get used against you is to shred them.
Shredding is an effective method that can help render your sensitive documents unusable. However, the process isn’t complete without combining it with digital protective measures such as encryption. It has a direct role in safeguarding digital data and it could help protect you from identity theft where shredding might fall short. So, when paired, shredding and encryption work hand in hand to ensure comprehensive protection of your personal data, both offline and online.
Digital Password Management
Managing your passwords in a digital environment requires diligence due to the perpetual risk of hackers and cyber-attacks. One of the most effective ways to maintain password security is via the utilization of security suites. These suites not only provide protection against viruses and malware, but they often come equipped with robust password management tools. The centralization and encryption of your passwords under one secure system make it less likely for your information to be breached and misused.
In today's technological era, Internet safety is quintessential. It's tempting to use simple, easy-to-remember passwords for all your accounts, but doing so makes you vulnerable to online criminals. To protect your digital identity, craft unique, complex passwords for each online account and change them periodically. By applying these password management strategies, you can significantly enhance your Internet safety and guard against identity theft.
Crafting Strong, Unique Passwords
Protecting your digital identity doesn't have to be complex. In fact, creating strong, unique passwords can go a long way towards achieving this goal. When considering password security, think about it being one of the keys to your cybersecurity, a defense tool against online threats and cybercrime.
A password should never be easy to figure out. This means avoiding obvious choices such as birthdays, anniversaries or names. Instead, opt for a combination of uppercase and lowercase letters, numbers and special characters. Each account you have should feature a unique password - never reuse them. By simply dedicating time to crafting secure passwords, you are taking steps towards protecting your digital identity and ensuring cybersecurity.
Password Security Checklist
In a world heavily reliant on technology, the protection of privacy is paramount. One effective method to shield from online threats is the diligent management of passwords. A password security checklist is an essential tool in this endeavor.
Such a checklist consists of numerous pointers that guide the creation, usage, and maintenance of strong passwords. This not only aids in personal privacy protection but also reduces the risk of falling prey to online threats. A mix of alphanumeric characters, use of both lowercase and uppercase letters, no repetition of passwords, and regular changes to login credentials are some of the critical components of a password security checklist.
The Importance of Password Variation Across Accounts
Maintaining unique passwords across all online accounts is crucial for effective digital security. Using the same password for multiple accounts increases the risk of identity theft. Once a cybercriminal gets access to one account, they can potentially use the same login details to breach other accounts. Therefore, if each account has a unique password, even if one account is compromised, the others will remain secure.
In the digital age, password variation is no longer an option but a necessity. When creating passwords, make sure each is distinct and complex, combining letters, numbers, and symbols which are hard to predict. Avoid obvious choices like birthdays, family names, or sequential numbers. Remember, your digital identity is only as secure as your weakest password.
Mobile Device and Online Security
In the present age, our lives have become inextricably linked with the advanced technology that obtrudes into our daily tasks. Smartphones, tablets and laptops have turned into indispensable tools, harboring a wealth of personal and financial information. This data remains vulnerable to cyber threats if not adequately safeguarded. To protect our digital ecosystem, it is paramount to employ stringent security measures on mobile devices and other online platforms.
Password protection is a fundamental aspect of securing devices and online accounts. Crafting robust, unique passwords is one practical way to defend against potential threats. Regularly updating mobile operating systems and applications could also thwart potential security breaches, as these updates often contain crucial security patches. Wi-Fi networks can pose another risk; when connecting to public Wi-Fi, encrypting communication through VPNs or avoiding sensitive transactions could significantly reduce exposure to nefarious activity.
FAQs
What is identity theft and how does it impact online security?
Identity theft is a criminal act where someone unlawfully obtains and uses another person's personal data, typically involving financial gain. It can lead to unauthorized transactions, ruined credit scores, and even legal troubles for the victim. It significantly weakens online security as it often involves the breaching of personal online accounts and data.
How can I protect myself from online scams such as phishing and fraud?
Protecting yourself from online scams involves staying vigilant and aware. Never open suspicious emails or click on unknown links. Always check the source of any email or message that asks for personal or financial information. Install reliable security software on your devices and keep them updated.
What can I do to protect my Social Security Number?
You should be very careful about who you share your Social Security Number with. Only give it out when absolutely necessary and to trusted entities. Never carry your Social Security card with you; instead, keep it in a secure place.
Why is it important to handle financial information responsibly?
Handling financial information responsibly is important to avoid any unauthorized access or misuse of your funds. This includes keeping your credit card, bank account numbers, and other financial documents secure.
What is the significance of shredding documents containing personal information?
Shredding documents with personal information prevents them from falling into the wrong hands. This can prevent identity theft and other types of fraud.
How does digital password management enhance online security?
Digital password management allows you to store and manage your various passwords securely. It can generate strong, unique passwords for your accounts, and you only need to remember a single master password.
What are the characteristics of a strong, unique password?
A strong, unique password consists of a mix of uppercase and lowercase letters, numbers, and special characters. It should be at least 12 characters long and avoid using personal information or common words.
Why should I use different passwords for different accounts?
Using different passwords for different accounts ensures that if one of your accounts is compromised, the others remain safe. It adds an extra layer of security and makes it harder for cyber criminals to gain access to all your accounts.
How can I enhance the security of my mobile device?
Enhancing the security of your mobile device can be done by regularly updating your operating system and apps, installing a reliable security software, using strong, unique passwords for your device and apps, and avoiding public Wi-Fi networks for sensitive transactions or data access.



Hi,
I intend to contribute a guest post to your website that will help you get good traffic as well as interest your readers.
Shall I send you the topics then?
Best,
Alvina Miller
Sure you can contact on support@techlooters.com